InnoDisk: All-in-One Blockchain Solution With InnoBTS SSD
Added hash strings are able to solve problem of blockchain scalability, in result of reducing time and cost while implementing blockchain technology to IoT devices.
This is a Press Release edited by StorageNewsletter.com on June 4, 2021 at 2:32 pmBlockchain is a new technology that is often used in the growing field of AIoT.
The process was developed for storing data in accounting to protect it from unauthorized access. Blockchain is also frequently used in connection with cryptocurrencies.
The technology is used whenever the stored information must be permanently correct, complete, and trustworthy, no matter how often it is accessed. In addition, the solution ensures that the data is securely protected from external influences.
As the name suggests, blockchain is a chain of data, with new chain parts – i.e., data blocks – being added all the time. This chain can be continued indefinitely by continuously appending new blocks to the end. The individual blocks are linked to each other by means of cryptographic chaining. This is done with the help of a hash value. In addition to its actual information, each block contains the hash value, i.e., the fingerprint of its predecessor, which clearly defines the sequence of the transaction data. In addition, a history of the transactions is created in this way, which increases data integrity.
Basically, with the blockchain, copies of the database are distributed among many users instead of being stored as a whole on a central server as is the case with a classic database. In this way, the blockchain ensures that the data is available at any time and from anywhere, whereas a traditional server can fail unexpectedly due to a defect in the Internet connection or hardware problems. With blockchain, the copies are also constantly updated and repeatedly compared with each other in order to protect the entire system from outside access and thus from manipulation.
Blockchain is considered highly tamper-proof. There are numerous copies of the chain, as all changes in the data are continuously distributed to all participants in the system. Thus, it is immediately noticeable if one of these copies has been manipulated. In comparison with the other distributed copies, it is quickly apparent which data records have been manipulated. Simultaneous manipulation of all distributed copies of the data records is almost impossible. This makes business processes more secure when converting to the blockchain.
Currently, applying blockchain technology on IoT devices still faces many challenges. If the standard blockchain is used, the bandwidth of transmissions is limited to 15 units per second, and upload times are delayed. It means to achieve blockchain on AIoT is still challenging. However, in the blockchain solution with InnoBTS SSD from InnoDisk Corp., the added hash strings are able to solve the problem of blockchain scalability, in the result of reducing the time and cost while implementing blockchain technology to IoT devices.
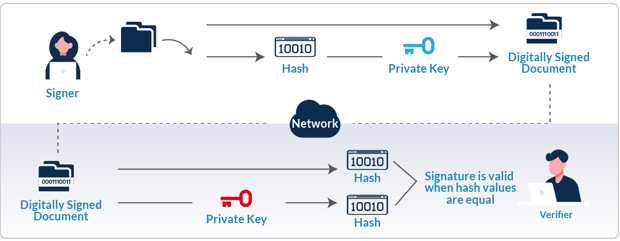
Normally, the data that is uploaded to the blockchain is visible to all users. When using the InnoBTS SSD, the hash string is created with a private key that is only available to the sender, and only the unintelligible hash string is visible to outsiders. In addition, the private key is well-protected in a safty zone with a hardware-based SSD structure.
By using the hash strings with InnoBTS SSD, extensive IoT data can shrink into a minimal amount of data and upload, therefore reducing costs. In addition, the integration of all functions into the SSD saves further costs by avoiding software implementation and compatibility issues.
IoT devices generate numerous data, and it is impossible to upload all those data on the blockchain, also difficult to enable data search and data analysis. Using InnoBTS SSD technology, IoT data can be defined as one root hash [i] that makes IoT data decreasing its cost on the blockchain, ensures data integrity, and simplifies data management.
In conclusion, the InnoBTS solves the bandwidth, cost, and management issues by packaging the IoT data into a short hash that is added to the chain. InnoBTS SSD creates a small hash string and circumvents the problems, in the result of reducing data transmissions as well as simplifying data search and analysis. Finally, the software-independent digital signature ensures that everything uploaded can be easily verified, while the data itself is only visible as an unintelligible hash string. Only the sender has the private key needed to extract the data from the hash string.













 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter

