CyberProtonics Data Protection Quantum-Resistant Software-Based Cryptosystem for Digital Ecosystem, IoT and Generative AI
End-to-end encryption renders breached data useless from most sophisticated cyberattacks of today and in future.
This is a Press Release edited by StorageNewsletter.com on March 15, 2024 at 2:01 pmSummary :
- Steal Now, Decrypt Later (SNDL) players are harvesting data ahead of post-quantum cryptography (PQC).
- CyberProtonics’ software-based cryptosystem uses a small code footprint with minimal computing resources to produce blistering-fast encryption speed.
- Embeddable anywhere – hybrid workforces, industrial infrastructure, IoT, streaming content, satellites, generative AI – for breach immunity without performance impacts.
CyberProtonics, trailblazers in quantum-resistant data protection, introduced a 1st lightweight, software-based cryptosystem that makes being quantum-ready easy, affordable, and practical.

Embeddable virtually anywhere, any time, the cryptosystem generates fast encryption speeds of 512 bits to up to 10,000 bits, rendering data useless when a breach occurs. The company also announced a major OEM agreement with Simplifi, providers in secure remote computing.
Legacy-friendly and plug-and-play features allow its cryptosystem to integrate in all types of applications, including IoT, e-sim, and generative AI Private Large Language Models (PLLMs). CyberProtonics protects data at rest and in transit, without performance impacts, and is recognized as 1st lightweight quantum-resistant commercial solution for rendering stolen data completely useless.
“Finally, we’re seeing an easy solution that provides end-to-end quantum-resistant encryption at rest and in transit to counter today’s pernicious cyberattacks and alleviate impeding Q-day fears,” said Chris Steffen, VP, Enterprise Management Associates.
Anywhere, anything, every time protection
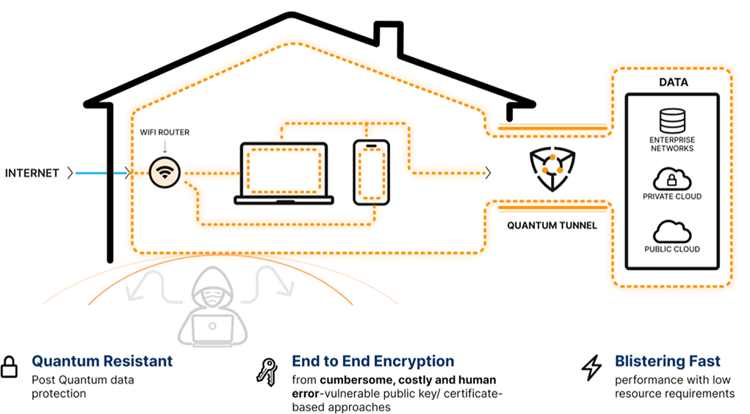
In today’s increasingly hostile cyber threat landscape, everyone should be protected from bad actors and malicious cyberattacks, wherever their data resides. The company’s solution adds an indispensable, affordable additional layer of quantum-resistant security at the source where data is created to protect legacy, current, and future cybersecurity system architectures, networks, and devices.
Among applications are:
- Work from home: Employees continue to work from home, and cybersecurity is more important than ever for the hybrid workforce. The company keeps confidential work data secure, at rest or in transit.
- IoT: The firm’s cybersecurity protocols protect IoT devices and networks from the latest threats with reliable and robust security.
- Generative AI: Large Language Models that companies want to keep private are protected by the company’ proprietary cryptosystem.
- Defense: 512-bit to 10,000-bit encryption protects data at rest or in transit in theaters of operations, supporting unmanned aerial vehicles (UAVs), wearable devices, connected vehicles, smart infrastructure, and portable communications.
- Satellite: End-to-end encryption in the ground terminal and in the satellite itself safeguards transmissions, ensuring data security and confidentiality.
- Industrial control panel: Protects critical infrastructure with next-gen quantum-resistance technology, designed to ensure reliable and resilient security for factories, power plants, and wastewater treatment facilities.
- Commercial data: Banking and finance, healthcare, hyperconnected commerce, and more.
 New era in data protection
New era in data protection
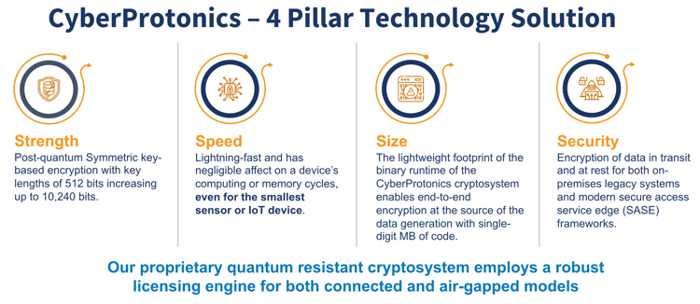
The firm’s proprietary software employs a licensing engine for both connected and air-gapped models and solutions, with varying time periods and iterations.
It delivers:
- Strength: Post-quantum symmetric key-based encryption, with key lengths of 512 bits, increasing up to 10,000 bits.
- Speed: Fast operation does not affect a device’s computing or memory cycles, even for the smallest sensor or IoT device.
- Size: The lightweight footprint of the company’ cryptosystem’s binary runtime enables end-to-end encryption at the data generation source, with single-digit megabyte of code.
- Security: Encryption of data in transit and at rest for both on-premises legacy systems and modern secure access service edge.
- Breach immunity and unwavering compliance: Valuable data is made useless. Full compliance with regulatory mandates and industry standards such as GDPR, HIPAA, PCI DSS, and SOX is automatic and assured.
- Market-proven SDK: Symmetric key encryption optimized for small footprint applications (crucial for IoT devices), stronger than any currently deployed application of AES, RSA, or ChaCha20. Fully automated key management that eliminates manual key distribution human errors. C language callable APIs.
Greg Welch, CEO and founder, CyberProtonics, said: “In a world where cybercrimes are an everyday occurrence, we’re on a mission to encrypt all data to ensure it never falls into the wrong hands, rendering breached data useless to malicious actors, hostile nation states and their proxies. Innovators, users, regulators, and OEMs need and deserve affordability, speed, and performance in data protection that’s accessible anywhere, any place, and protects every time. CyberProtonics immediately turns the organization’s diamonds of data into coal, unusable by anyone except those intended.”
Resources:
Graphics: CyberProtonics – 4 Pillar Technology Solution; Product – Market Fit
Blog: How is CyberProtonics Tackling the Cybersecurity Challenge of Working from Home?
Blog: The Inevitable Cyber Breach: It’s Not a Question of ‘If’ Anymore
Simplifi Selects CyberProtonics for Work From Home Advanced Cybersecurity – Immediately Renders Hacked Data Unusable, Delivers First WFH Quantum Readiness
About CyberProtonics:
CyberProtonics is at the forefront of cybersecurity, offering a fast, robust quantum-resistant, software-based cryptosystem. The company render data useless to malicious actors with end-to-end encryption that is easy to adopt and effortlessly integrates into your existing systems. Ideal for a wide range of diverse applications from IoT to complex databases, the firm’s cryptosystem safeguards information in transit and at rest without compromising on speed or performance. From today’s malicious ransomware to tomorrow’s quantum computing, hackers are completely disarmed with CyberProtonics.












 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter


