Synology Security Advisory SA-21:30 Log4Shell
Concerning log4j 2 vunerability
This is a Press Release edited by StorageNewsletter.com on December 15, 2021 at 2:01 pmSynology, Inc. has published a security advisory concerning Log4Shell vulnerability.
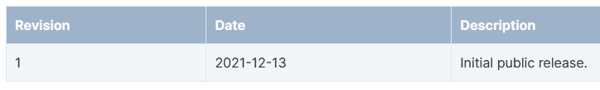
Publish time: 2021-12-13 18:29:31 UTC+8
Last updated: 2021-12-13 18:29:31 UTC+8
Severity: Not affected
Status: Resolved
Abstract
None of Synology’s products are affected as CVE-2021-44228 only affects products equipped with log4j 2.
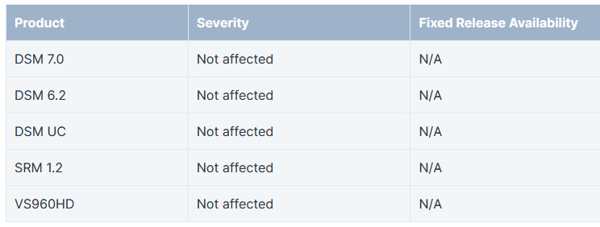
Affected products
Mitigation: None
Detail: CVE-2021-44228
Severity: Not affected
CVSS3 base score: 0.0
CVSS3 vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:N
Apache Log4j2 <=2.14.1 JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. In previous releases (>2.10) this behavior can be mitigated by setting system property ‘log4j2.formatMsgNoLookups’ to ‘true’ or it can be mitigated in prior releases (<2.10) by removing the JndiLookup class from the classpath (example: zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class).
Reference
Revision











 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter


