Ctera Adds Data Exfiltration Prevention to Ransom Protect
Launches honeypot decoy capabilities to address data extortion and insider threats.
This is a Press Release edited by StorageNewsletter.com on April 19, 2024 at 4:03 pmCtera enhanced Ransom Protect, with active protection vs. data exfiltration using honeypot techniques.
This addition bolsters enterprises’ defenses vs. insider threats and the latest extortion tactics employed by ransomware perpetrators.
Double extortion, a tactic that combines data exfiltration and encryption, has become a widespread method used by cybercriminals in ransomware attacks. Threat actors first exfiltrate sensitive information from their targets before launching the ransomware encryption routine, subsequently demanding a ransom payment to regain access to the encrypted assets and threatening to publicly expose the stolen data if the demand is not met promptly.
Ransom Protect is an AI-powered cyber defense engine integrated into the Ctera global file system, providing zero-day protection vs. widespread ransomware attacks. The strong demand for Ransom Protect contributed to firm’s record-breaking results in 2023, solidifying the company’s position as a leader in Cyberstorage and earning it a leadership position in GigaOm’s Sonar Report for File-Based Primary Storage Ransomware Protection.
Now enhanced with honeypot capabilities, Ransom Protect utilizes the strategic deployment of decoy files within the organization’s file system and enables the firm to identify and stop unauthorized access or attempts at data theft, effectively neutralizing threats before significant damage can occur.
“Data exfiltration poses a severe risk to organizations, as threat actors can leverage stolen sensitive information for extortion, causing immense financial and reputational damage,” said Oded Nagel, CEO, Ctera. “With our new honeypot functionality as part of Ransom Protect, we are providing our customers robust active defense vs. these pernicious attacks, ensuring the protection of their valuable data assets.”
Key features of Ransom Protect include:
- Data Exfiltration Prevention: Decoy files enable real-time detection and blocking of data exfiltration attacks.
- Real-time AI Detection: Advanced ML algorithms identify behavioral anomalies suggesting fraudulent file activity, and block offending users withins.
- Zero-Day Protection: Does not rely on traditional signature update services.
- Incident Management: Administrator dashboard enabling real-time attack monitoring, comprehensive incident evidence logging and post-attack forensics.
- Instant Recovery: Near-instant recovery of any affected files from snapshots that are securely stored in an air-gapped, immutable cloud object storage effectively thwarting any manipulation attempts by malicious actors.
- One-Click Deployment: Single-click feature activation on Ctera Edge Filers with latest version release.
With the introduction of Ransom Protect with honeypot, the vendor reinforces its commitment to delivering Cyberstorage solutions that address the evolving threats faced by modern enterprises, safeguarding their critical data assets from malicious actors.
Comments
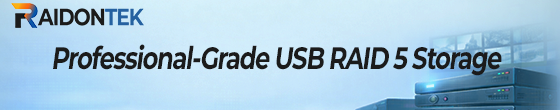
Ctera continues to lead the category with a well-established solution well deployed and adopted WW, cases studies speak for themselves in various industries and vertical market segments. The 2 other leaders also bring compelling solutions and the battle is hot between them. These 3 players are clearly detached from followers in various analyst reports.
Click to enlarge
2023 was a stellar year for Ctera with a growing business, new partnership such the one with Hitachi Vantara and key product features in the cyber resiliency domain.
Click to enlarge
The company unveiled 3 interesting services, the one described above with ransomware protection, the 2nd iteration of Vault and the notification service.
The ransomware protection, introduced last year, is now extended with AI and super fast protection and the honeypot capability to prevent data exfiltration and extraction fully integrated and easy to enable on the edge filer level.
Vault 2 extends WORM Cloud Folders with more granular control working at the file and object level with legal hold, object lock and chain of custody. The notification service adds the information of events on files with ability to "follow" events.
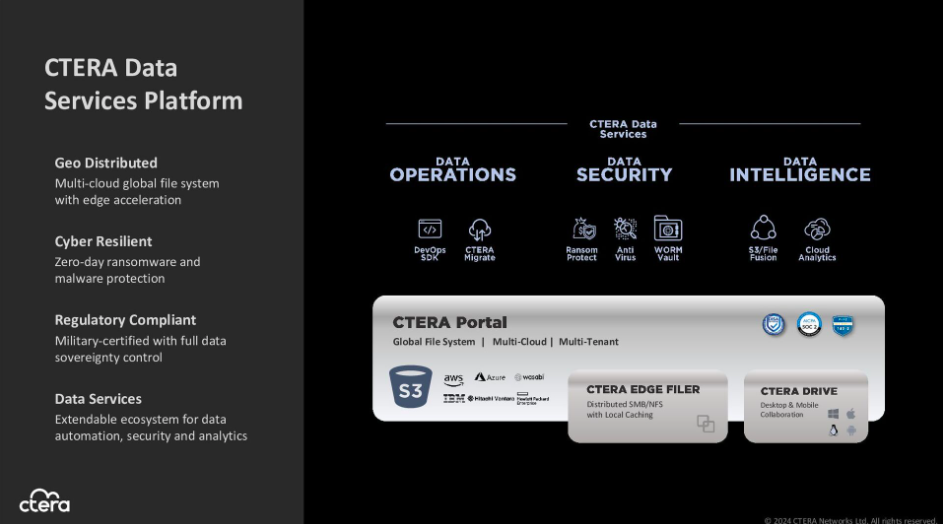
The firm also developed a data intelligence service leveraging AI with LLMs to provide a real-time monitoring and control that is even more critical on the cyberthreat and risk pressure.
Click to enlarge












 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter


