Continuity Joins Dell Extended Technologies Complete Program
To help protect customers’ storage and data protection systems
This is a Press Release edited by StorageNewsletter.com on June 1, 2023 at 1:00 pmContinuity Software Ltd, an Israeli provider of storage and backup security solution, has joined the Dell’s Extended Technologies Complete (ETC) program.
Storage is becoming a prime target of cyber-criminals as they attempt to infiltrate the enterprise. Faced with a wall of perimeter defenses, security safeguards, and well-patched operating systems and applications, storage and backup systems are front and center in the fight vs. ransomware.
According to Gartner1, “Most ransomware attacks target unstructured datasets on network shares, making centralized file storage solutions an attractive target for encryption and/or data exfiltration of large amounts of data.”
The storage attack surface is broader and deeper than many CISOs might suspect. It is tempting to think that storage security concerns could simply be resolved by patching clients (Host OSs) and making sure there’s a backup solution in place. However, cyber-criminals can breach storage systems in a number of creative ways.
In the 2023 State of Storage & Backup Security Report, top 5 security risks are identified:
- Insecure network settings
- Unaddressed CVEs
- Access rights issues (over-exposure)
- Insecure user management and authentication
- Insufficient or incorrect logging and auditing
For each risk, the firm has outlined the business impact. This helps to demonstrate how cyber-criminals can get through the parameter to the storage or backup environments.
It’s not just ransomware that’s top of mind for security and storage teams. Auditors and cyber insurance firms are taking a much closer look at the security of storage and backup systems, as well as regulatory bodies and industry standards.
NIST Special Publication 800-209; Security Guidelines for Storage Infrastructure: “Periodically and proactively assess configuration compliance to storage security policy.”
And ISO 27001, published in November 2022, includes the following instruction: “Backup copies of information, software and systems shall be maintained and regularly tested in accordance with the agreed topic-specific policy on backup.”
Hardening Dell Storage and Data Protection Systems – with StorageGuard
Dell Technologies, Inc. is at the forefront of protecting customers’ evolving environments through its PowerProtect portfolio. Through ETC program, Dell customers can add StorageGuard, to complement their Dell storage and data protection solutions, helping them keep systems secure and compliant. StorageGuard scans customer environments to ensure they are secure and follow all relevant vendor, industry and regulatory best practices.
StorageGuard enables Dell customers to have visibility of all security misconfigurations and vulnerabilities in their storage and data protection environment, while hardening these critical systems and guaranteeing compliance with security regulations and industry standards.
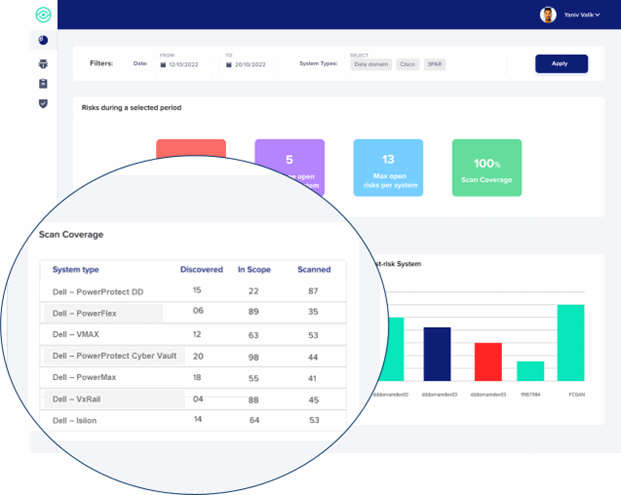
In addition to detecting and remediating security risks across Dell’s storage and data protection systems, StorageGuard also validates configuration and best practices for Dell PowerProtect Cyber Recovery Vault for isolated recovery, ensuring it is air-gapped, isolated, and hardened.
The ETC Program underscores company’s commitment to offer customers flexibility and choice with complimentary solutions such as StorageGuard for protecting their critical systems from cyberattacks and insider threats.
“Being invited into Dell’s ETC program is a great honor,” said Gil Hecht, CEO, Continuity. “It also testifies to the powerful value proposition StorageGuard delivers – the ability for Dell customers to assess their vulnerability to cyberattacks and get visibility of security risks across their storage and data protection environments.”
StorageGuard improves the ransomware-readiness and overall security posture of storage and data protection environments. The solution reduces the effort required by ops teams and admins to develop and enforce security policies, prove compliance for audit, and chase down false positive CVE alerts raised by tools that aren’t storage-aware.
1 Gartner: Innovation Insight for Cyberstorage Solutions to Protect Unstructured Data Against Ransomware, 8 October 2021.











 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter