Apacer CoreSecurity2 Integrating Four Security Protection Technologies for SSDs
Protecting companies working remotely during Covid-19
This is a Press Release edited by StorageNewsletter.com on May 22, 2020 at 2:23 pmDue to the global impact of the Covid-19 epidemic, many companies are in work-from-home mode.
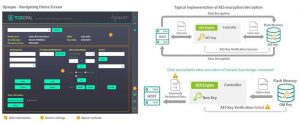
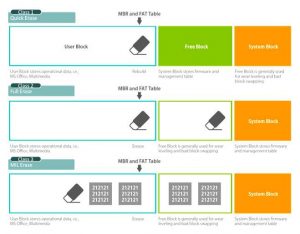
Since a large number of employees may need to log in to the company network remotely and use cloud applications, enterprises may be facing new security threats for the first time. Considering the large volume of data transmission in the 5G era and the high requirements of enterprises for security protection, Apacer Technology, Inc. created the CoreSecurity2 technology, integrating 4 security protection technologies for SSDs.
Coresecurity2 encrypting
Click to enlarge
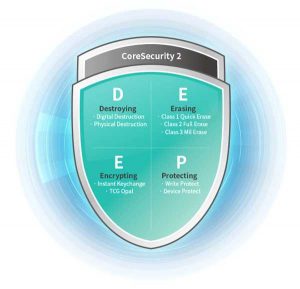
These include: destroying hardware and software if necessary, erasing data thoroughly, encrypting data when reading and writing it, and protecting drives from unauthorized access. This approach delivers security. It’s for enterprises who need access to close security holes that may have been opened by transitioning to work-from-home mode.
Instant Keychange
4 approaches to strengthening security for software, hardware and firmware
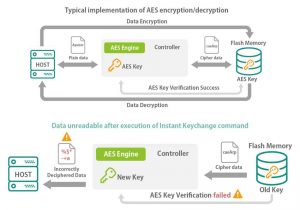
To better meet the security requirements of enterprise customers, the company’s industrial-grade SSDs can be shipped with CoreSecurity2 already built in. Take server and networking applications as an example. They will benefit from the encryption upgrades that CoreSecurity2 includes. By adhering to the TCG Opal 2.0 spec, the firm uses the AES 128 and 256 protocols to encrypt all data as its written to the SSD. In addition to providing security, this approach also allows users to send an Instant Keychange trigger command. This is done only when a drive is going to fall into the hands of a bad actor, and will destroy the original security key and replace it with a new one in less than a second. The result is that the data can no longer be decrypted, and the bad actor will be completely unable to access confidential information.
Coresecurity2 Erasing
Click to enlarge
CoreSecurity2 contains 3 more technologies. In a similar way to the case described above, if a drive is about to fall into the hands of a bad actor, the user may wish to destroy it quickly and effectively to prevent sensitive data from falling into unknown hands. The Destroy function makes this possible. There are multiple ways to carry this out, including both physical and digital destruction methods, and the command can be sent via software or hardware. The Erase function also provides multiple erasure options. In addition to quick and standard erase functions, military-grade overwriting can also be performed.
And the Protect function is useful as well, since it can prevent unauthorized data tampering or writing to the HDD. For industrial, defense and healthcare applications that require high sensitivity and confidentiality of data, CoreSecurity2 improves security at the software, hardware and firmware levels.
Click to enlarge
Meeting Demanding Specs in Variety of Interfaces
In addition to its features, CoreSecurity2 is popular among international manufacturers because it is available in a variety of specs. Industrial-grade SATA and PCIe interfaces are available, and models that can tolerate wide temperature swings and challenging operating environments are ready to ship as well. This means manufacturers serving the defense and healthcare industries can market these value-adding features to their discerning customers. The company carries out internal testing to ensure every SSD can deliver reliability and durability.
Resource:
Video: CoreSecurity2 – A proprietary data protection technology to elevate the data security level
Read also:
Apacer and Advantech Collaborate on IoT Development
Integrating IoT cloud-based applications to make smart factories more efficient
March 3, 2020 | Press Release












 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter


