75% of Used Drives Purchased From Amazon, eBay and Gazelle Have Unsuccessful Deletion Attempts Previously Made
Blancco and Kroll Ontrack study finds
This is a Press Release edited by StorageNewsletter.com on October 14, 2015 at 2:39 pmA data security study from Blancco Technology Group and Kroll Ontrack, Inc. found varying amounts and types of residual data on used mobile devices, HDD drives and solid state drives purchased online from Amazon, eBay and Gazelle.com.
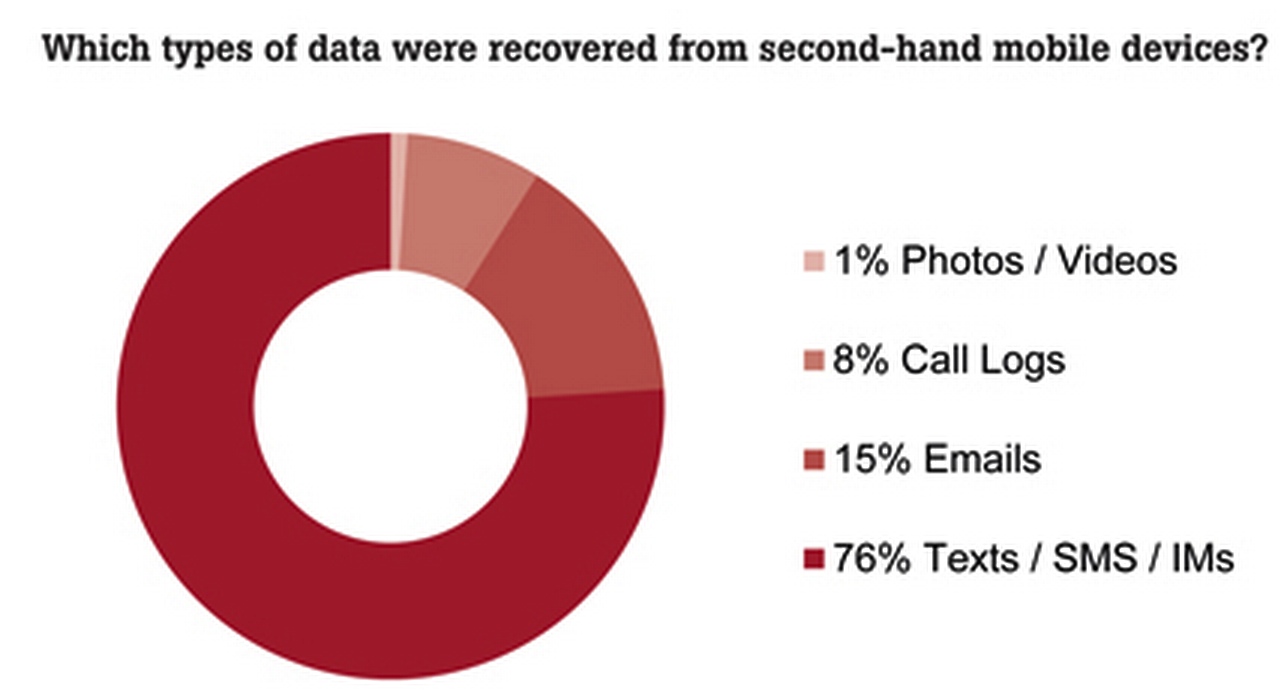
Based on an examination of 122 pieces of second-hand equipment, 48% of the HDDs and SSDs contained residual data, while thousands of leftover emails, call logs, texts/SMS/IMs, photos and videos were retrieved from 35% of the mobile devices.
Upon closer examination, it was discovered that a deletion attempt had been made on 57% of the mobile devices and 75% of the drives that contained residual data. Even more compelling was the discovery that those deletion attempts had been unsuccessful due to common, but unreliable methods used, leaving sensitive information exposed and potentially accessible to cyber criminals.
As Paul Henry, IT security consultant, Blancco, explains: “Whether you’re an individual, a business or a government/state agency, failing to wipe information properly can have serious consequences. One of the more glaring discoveries from our study is that most people attempt in some way or another to delete their data from electronic equipment. But while those deletion methods are common and seem reliable, they aren’t always effective at removing data permanently and they don’t comply with regulatory standards. There’s no better example of this danger than the findings of a recent state audit, which found that 12 US state agencies responsible for handling taxes, programs for people with mental illness and driver’s licenses used inadequate methods to attempt to wipe information. The big lesson for both businesses and consumers is to understand which deletion methods are effective and comply with regulatory standards and, most importantly, to be cautious of blindly trusting that simply ‘deleting’ data will truly get rid of it for good.”
Another startling finding was that the residual data left on two of the second-hand mobile devices were significant enough to discern the original users’ identities. Whether it’s a person’s emails containing their contact information or media files involving a company’s intellectual property, lingering data can have serious consequences. Together, all of the study’s findings serve as a powerful warning about the importance of using effective data erasure methods and the need to mitigate security risks that may occur when done improperly or incompletely.
“Manually deleting data or simply logging out of a mobile device app does not erase data from the device,” explains Todd Johnson, VP of data recovery operations, Kroll Ontrack. “Deleting data simply hinders the ability for the mobile device to locate the data – the actual data still remains and can be recovered. In the case of HDDs and solid state drives, formatting to securely delete data can lead to varying results as each OS performs the action differently. To successfully delete data to a state where it cannot be recovered, one must completely overwrite the data using reputable deletion software.”
Additional findings from the study include:
- 122 second-hand mobile devices and drives were purchased in the U.S., Germany and the U.K. on eBay, Amazon and Gazelle
- 16% of this number were mobile devices (20), 73% HDDs and 11% solid state drives (102)
- 46% of the 122 total devices contained residual data
Mobile device key findings:
- Data is difficult to delete and can easily resurface after mobile devices are resold. 57% of the mobile devices with residual data found on them had a deletion attempt made on them, which left 179 texts, 252 instant messages, 75 large photos and two SMS messages exposed.
- Leftover emails, text messages and instant messages can cause personal, financial and reputational damage to users and their employers. A total of 2,153 emails and 10,838 texts/SMS/instant messages were retrieved from the mobile devices analyzed.
- In 2 instances, the identities of original owners were determined based on data recovered from re-sold mobile devices
- Samsung, HTC, Apple, Motorola and LG mobile devices were all included in the study
HDDs, SSDs key findings:
- Basic file-deletion commands leave HDD users with a false sense of security. On four of the drives containing residual data, or 11%, only a basic delete was performed, meaning that the user simply deleted the file or sent it to the recycle bin. This left 444,000 files exposed.
- ‘Quick format’ and reformatting are common, but unreliable, tactics to wipe personal information clean from old HDDs. Our analysis showed that ‘quick format’ had been performed on 61% of the drives with data still present.
- 48% of the 102 drives purchased still had data intact
- A deletion attempt was conducted on 75% of those drives that still contained data
- 25% were re-sold without any type of deletion attempt








 Subscribe to our free daily newsletter
Subscribe to our free daily newsletter
